Infoblox and Confiant Uncover the Industrialized Abuse of Commercial Trackers in the Global Fraud Ecosystem
In the world of modern cybercrime, cloaking has evolved from a niche evasion tactic into a foundational block of criminal infrastructure. New longitudinal research from Infoblox Threat Intel and Confiant has exposed a massive operation involving approximately 15,500 domains abusing Keitaro, a popular advertising performance tracker, to facilitate AI-branded investment scams and malware delivery.
The research highlights a significant shift in threat actor behavior: instead of building bespoke malicious infrastructure, criminals are purchasing or pirating commercial software like Keitaro Tracker.
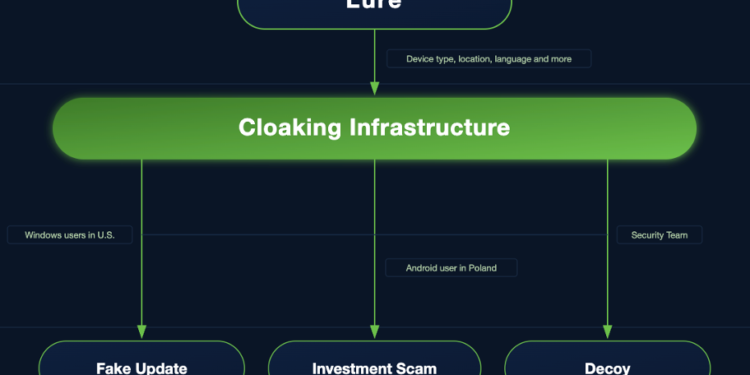
Because these tools are designed for high-performance marketing, they offer built-in Traffic Distribution Systems (TDS) that allow attackers to cloak their activity, showing benign content to security researchers and automated scanners while routing potential victims to malicious landing pages.
The study identifies a surge in investment scams that leverage the current AI gold rush. These campaigns use the promise of Smart AI Trading Technology to lure victims, often using:
- Deepfake Imagery: Programmatically generated visuals to establish false credibility.
- Generative AI Copy: Headlines and visuals mass-produced to create high-velocity, rotating lure pages.
- Predictable Greed: Promising outsized returns through automated intelligence to bypass the victim’s natural skepticism.
By combining DNS-level visibility with advertising chain analysis, the joint research team was able to map an ecosystem that spans compromised websites, social media, and legitimate online advertising networks.
“The story really isn’t about one specific tool; it’s about an ecosystem that malicious actors are using to scale and target attacks around the globe,” says Dr. Renée Burton, VP of Infoblox Threat Intel. “Cloaking allows them to evade restrictions and shield themselves from the very security community trying to track them.”
For enterprise security leaders, this research proves that looking for malware is no longer enough. Organizations must now account for the abuse of legitimate SaaS and marketing tools that provide criminals with readymade, high-availability infrastructure. As generative AI makes scam production easier, the ability to identify and block the underlying TDS and Cloaking mechanics will be the primary line of defense.